Overview
Understanding the vulnerabilities of your WiFi network can be challenging as users can easily create networks on demand, or even perhaps unintentionally. But as recent events have demonstrated, scanning your WiFi network is an important part of understanding your security posture.
Most vulnerability assessment tools simply take their current network scanners and point them at the wireless infrastructure. This approach does not give you the information that is unique to wireless networks. Immunity has built the first automated, WiFi specific, vulnerability assessment and penetration tool.

Unlike traditional scanners that merely identify possible vulnerabilities, SILICA determines the true risk of a particular access point. SILICA does this by unintrusively leveraging vulnerabilities and determining what assets behind the vulnerable access point can be compromised.
Additionally while traditional scanners can enumerate the vulnerabilities of a particular target, they cannot evaluate whether a mitigating control is in place on the target or in the surrounding environment. With SILICA’s unique methodology it can report on whether a vulnerability can be successfully exploited.
 More than simple scanning, the benefits of using SILICA include:
More than simple scanning, the benefits of using SILICA include:- Improved security posture
- Simplified trouble shooting
- Network mapping
- Create real threat profiles and vulnerability assessments
- Build WiFi risk and vulnerability analysis for PCI, SOX
- Rogue access point detection
- Auditing wireless client security
With SILICA You Can:
- Recover WEP, WPA 1,2 and LEAP keys
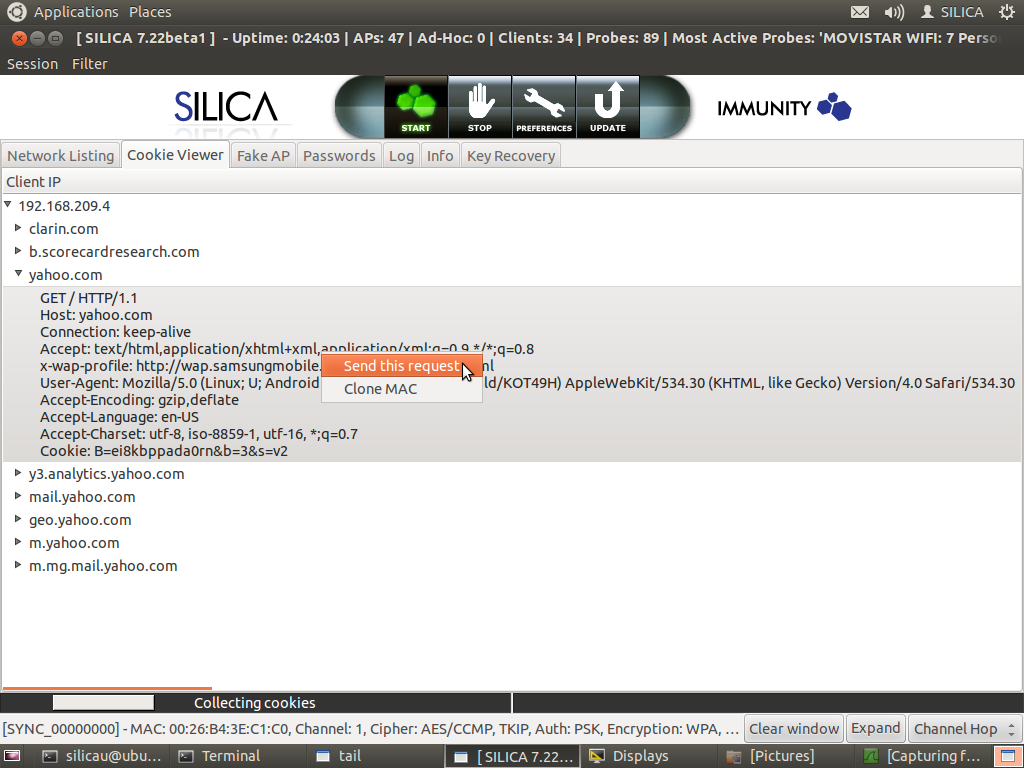
- Passively hijack web application sessions for email, social networking and Intranet sites.
- Map a wireless network and identify its relationships with associated clients and other access points.
- Identify vendors, hidden SSIDs and equipment passively.
- Scan and break into hosts on the network using integrated CANVAS exploit modules and commands to recover screenshots, password hashes and other sensitive information.
- Perform man-in-the-middle attacks to find valuable information exchanged between hosts.
- Generate reports for wireless and network data.
- Hijack wireless client connections via access point impersonation.
- Passively inject custom content into client's web sessions.
- Take full control of wireless clients via CANVAS's client-side exploitation framework (clientD).
- Decrypt and easily view all WEP and WPA 1/2 traffic.
HIPAA Typical SILICA users include:
- Forensics teams working to re-create an incident.
- Security Management teams that want a purpose-build vulnerability scanning and exploitation tool for their WiFi network, including remote identification of systems and mobile devices even when running personal firewalls.
- Network administrators who want to discover ad-hoc, unauthorized clients, or weakly authenticated WiFi access points, and to test/recover WEP, LEAP and WPA 1,2 keys.
- Compliance officers looking for real risk management profiles.
- Security Assessment teams that are tired of the false positives from traditional scanners use SILICA's man-in-the-middle and aggressive remote exploitation capability.
SILICA Product Features
- Access Point recon and analysis
- Automated client discovery
- Access Point exploits
- Automated exploit launch and run
- Automated SSID discovery
- WEP, WPA 1/2 and LEAP credential recovery
- WPS attacks, including offline bruteforcing
- Man-In-The-Middle capability
- Fake AP attacks, including KARMA, SSL-Strip, Spoofed Certificates and Service Impersonation
- Browser Session Hijacking
- Number of hosts analyzed simultaneously: 256
- Average time to compromise a host: < 1 minute
- Average time to break a WEP network: 10 minutes
- Average time to break a LEAP, WPA 1/2 network: depends on key strength
- Report Format: HTML, DOCX
- Report retrieval: USB
- Frequency ranges: 802.11 a/b/g/n
- Installation: Virtual Machine
- Wireless cards: Panda Wireless PAU09 N600 Dual-Band Wireless USB Adapter (included)
SILICA leverages Ubuntu 16.04 LTS 64bit and is supplied as a virtual machine.
Included with SILICA there is a high performance Panda Wireless USB adapter that greatly increases the wireless performance over the base WiFi chip sets that are included in most commercial laptops.
This self-contained solution provides support for 802.11 a/b/g/n networks. This product is ideal for security personnel who wish to integrate WiFi testing into an existing test platform with our security testing tools.
SILICA VIDEOS
See SILICA in action by watching the latest videos from Vimeo.
For product questions or purchase information
please contact us
866-524-4782 *
imu.sales@appgatedotcom

